TL;DR
A Kerberoasting attack exploits the Kerberos authentication protocol by extracting service account tickets from Active Directory to crack their passwords offline. Organizations can defend against this threat by enforcing long, complex passwords, implementing Managed Service Accounts, and utilizing real-time monitoring to detect unusual ticket requests.
A kerberoasting attack is one of the most common and effective post-exploitation techniques used to compromise Active Directory (AD). By exploiting how the Kerberos protocol handles service tickets, attackers can harvest account credentials without ever sending a single packet to the target system. Because kerberoasting targets service accounts, which often have high privileges and weak passwords, it is a high-priority threat for IT security teams.
In this guide, we break down the anatomy of the attack and provide actionable strategies for detecting kerberoasting before it leads to a full domain compromise.
Active Directory (AD) is the beating heart of many organizations, IT infrastructures, managing user accounts, permissions, and access to critical resources. However, beneath its seemingly impenetrable exterior lies a vulnerability that attackers are increasingly exploiting: the Kerberoasting attack. Let’s take a look at this threat, understand its mechanics, and uncover why Active Directory is a prime target.
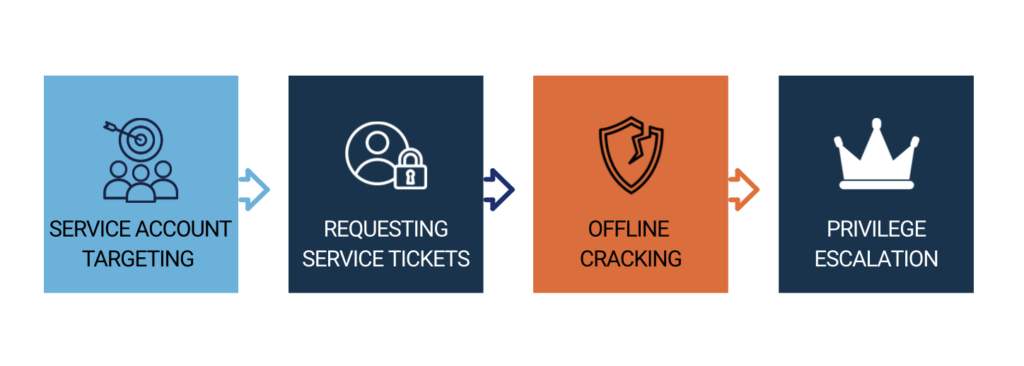
At its core, a Kerberoasting attack is an exploitation of the Kerberos authentication protocol, which is the backbone of Active Directory security. Here’s a simplified breakdown of a Kerberoasting attack:
Over 80% of breaches involve brute force or the use of stolen credentials — Kerberoasting directly exploits weak service-account credentials.
Active Directory, by design, is built on trust relationships due to its reliance on legacy Kerberos configurations. Kerberos relies on the security of passwords to protect service tickets. The exploit doesn’t require administrative rights to initiate, making it a “low-hanging fruit” for attackers.
The risk is compounded by:
The consequences of a successful Kerberoasting attack can be severe. Attackers can leverage compromised service accounts to move laterally within the network, gaining access to sensitive data, intellectual property, and financial information. In a worst-case scenario, they can elevate their privileges to domain administrator, effectively taking control of the entire Active Directory domain.
The fallout from such a breach can include financial losses, reputational damage, and regulatory fines. Furthermore, recovering from a Kerberoasting attack can be costly and time-consuming, disrupting business operations and eroding stakeholder trust.
Understanding the threat of Kerberoasting is the first step toward protecting your Active Directory environment. Cayosoft Guardian offers extensive visibility into service account activities, enabling you to identify suspicious behavior and potential Kerberoasting attempts before they escalate.
While the stealthy nature of Kerberoasting attacks can make them difficult to detect, there are signs within Active Directory that can alert you to an ongoing breach. By proactively monitoring these indicators, you can catch attackers in the act and prevent them from inflicting significant damage.
Event logs serve as your first line of defense in detecting Kerberoasting attacks. Active Directory logs various events, such as Kerberos service ticket requests (Event ID 4769), which can be monitored to spot unusual patterns indicative of an attack in progress. Key indicators include:
The median time attackers remain undetected is still measured in days. Proactive kerberos monitoring is the only way to shorten this window and stop a breach in progress.
Successful kerberoasting detection depends on your ability to distinguish a legitimate Ticket Granting Service (TGS) request from an exploit. Because the Kerberos protocol uses TGS tickets to authenticate users to specific services, an attacker must request these tickets before they can begin the offline cracking process. To catch them, you must monitor for an abnormal volume of TGS-REQ packets, particularly those targeting high-privilege service accounts with active Service Principal Names (SPNs).
Effective kerberoasting detection requires not only scheduled scans for extensive gap analysis in Active Directory and Entra ID but also real-time monitoring of changes that may indicate immediate threats. For example, if a standard user account suddenly requests dozens of tickets for SQL or Exchange services within seconds, it is a clear sign of a service account scan. Cayosoft Guardian‘s threat module is specifically designed to address both needs effectively. It offers real-time alerts for suspicious activities, such as password spray attacks (a common component of Kerberoasting) by continuously monitoring for signs that indicate such exploits. This dual approach ensures that you are equipped to quickly respond to emerging threats and protect your critical assets.
Detecting Kerberoasting attacks is crucial, but prevention is the ultimate goal. Let’s explore some proven strategies to safeguard your Active Directory setup against Kerberoasting attacks.
The simplest yet most effective defense against Kerberoasting is to enforce strong password policies for all service accounts, including the following specifics:
While strong passwords may seem like a basic precaution, they are often overlooked in the context of service accounts. They represent a significant barrier to attackers attempting to crack service tickets.
Service accounts are often the “weakest link” in kerberoasting because they are frequently over-privileged and poorly monitored. Implementing proper service account hygiene is crucial but challenging, as they are essentially user accounts that may not be easily identifiable by native tools. Cayosoft Administrator provides robust user management and reporting functions that are vital for maintaining account hygiene. It helps to:
Cayosoft Administrator not only assists in maintaining optimal service account hygiene but also provides seamless management across both Active Directory and Entra ID, ensuring a strong defense against potential security threats.
In healthcare organizations, Kerberoasting poses a unique and dangerous threat. Service accounts are often tied to essential clinical systems like EHRs, lab integrations, and imaging software, making them high-value targets for attackers. If compromised, these accounts could grant unauthorized access to sensitive patient data or disrupt care delivery. Cayosoft’s healthcare identity management solutions are purpose-built to address these challenges, helping IT teams enforce strong service account controls, identify misconfigurations, and monitor changes across Active Directory in real time, all while supporting compliance with data privacy regulations like HIPAA.
Compromised service accounts are a frequent cause of healthcare breaches. These accounts can expose EHRs and clinical systems if not tightly controlled.
MSAs offer a technical solution to the challenge of managing service account passwords. Unlike standard service accounts, MSAs do not have a password that a human knows or manages. Windows automatically handles the password generation and rotation (using complex 240-byte passwords) at the Domain Controller level. This not only enhances security but also reduces the administrative burden on IT teams. While MSAs are not a silver bullet, they can be a valuable addition to your Kerberoasting defense strategy.
While the previous strategies focus on specific tactics to deter Kerberoasting attacks, a comprehensive approach to Active Directory security is essential for long-term resilience. A holistic perspective lets you create a multi-layered defense that both thwarts Kerberoasting and strengthens your overall security.
Regular security audits and assessments are like routine checkups for your Active Directory environment. They provide valuable insights into potential vulnerabilities, including weak passwords, misconfigured service accounts, and excessive permissions.
By conducting both internal and external assessments, you can identify accounts with registered SPNs that haven’t been rotated in years. Identifying these weaknesses early allows you to remediate them before an attacker can request a service ticket for offline cracking.
The principle of least privilege (PoLP) is a fundamental security concept that emphasizes granting users and service accounts only the minimum necessary permissions to perform their tasks. By adhering to PoLP, you minimize the potential damage an attacker can inflict if they compromise an account.
Review the permissions assigned to each service account and remove any unnecessary privileges. Implement role-based access control (RBAC) to further refine permissions and ensure that users and service accounts have access only to the resources they need. With RBAC, even if an attacker successfully cracks a service account password, their ability to move laterally or escalate to Domain Admin is strictly limited.
Despite your best efforts, there’s always a chance that an attacker may successfully execute a Kerberoasting attack. Having a well-defined incident response plan in place can significantly reduce the impact of a breach.
Your incident response plan should include the following:
The average cost of a U.S. data breach is in the multi-million-dollar range. Preventing Kerberoasting and account compromise is far cheaper than remediation.
Cayosoft Guardian not only helps with detecting and preventing Kerberoasting attacks but also provides tools and resources to streamline incident response and recovery, including granular and automated rollback capabilities that protect objects from unwanted changes and surpass native Active Directory rollback. By integrating Cayosoft Guardian into your security strategy, you can enhance your overall resilience to cyber threats.
Protecting your organization against Kerberoasting attacks is a critical component of Active Directory security, but it’s only one piece of the puzzle. To truly safeguard your organization’s data, you need a multi-faceted approach that addresses a wide range of threats and vulnerabilities.
Cybersecurity is constantly evolving, with new threats and attack vectors emerging regularly. To maintain a robust defense, continuous monitoring and adaptation are essential. This means not only keeping abreast of the latest security trends and vulnerabilities but also proactively adjusting your security measures to address them.
Regularly review and update your security policies, procedures, and technologies to ensure that they remain effective against the latest threats. Implement a security information and event management (SIEM) solution to aggregate and analyze logs from various sources, providing a centralized view of your security posture.
Cayosoft Guardian is your protection against Active Directory threats, including Kerberoasting attacks. It continuously monitors your identity infrastructure, providing automatic threat detection and enabling swift incident recovery. Cayosoft Guardian allows organizations to proactively identify and mitigate security risks, gain insights into suspicious activity, enforce strong password policies, and ensure compliance, all while streamlining security management.
Ready to see Cayosoft Guardian in action? Schedule a demo today and discover how it can elevate your Active Directory security posture.
Kerberoasting attacks cleverly exploit a combination of factors inherent to Active Directory. First, the Kerberos authentication protocol, while robust, relies on the strength of passwords protecting service tickets. Second, Active Directory environments often house a multitude of service accounts, many with privileged access, making it challenging to maintain strong, unique passwords for each one. This creates fertile ground for attackers to request and crack these service tickets, ultimately gaining unauthorized access.
While completely eliminating the risk of Kerberoasting attacks is difficult, proactive measures can significantly reduce your vulnerability. Enforcing strong password policies for service accounts, implementing regular audits and assessments, and adhering to the principle of least privilege can create a multi-layered defense that makes it significantly harder for attackers to succeed. Solutions like Cayosoft that automate password management and provide real-time monitoring can further bolster your defenses.
Early Kerberoasting detection is crucial for minimizing the impact of a Kerberoasting attack. Actively monitor Active Directory event logs to identify telltale signs of an attack, like unusual service ticket requests, repeated failed login attempts for service accounts, or an abnormal volume of TGS requests.
While Kerberoasting is a significant threat, it’s not the only one facing Active Directory. Other attacks (like Golden Ticket, Silver Ticket, and DCSync) also target Kerberos vulnerabilities. A comprehensive Active Directory security strategy should encompass a broad range of protective measures, including strong password policies, regular audits, access controls, and proactive monitoring.
Cayosoft offers a suite of Active Directory security solutions designed to mitigate the risk of Kerberoasting attacks. It offers automated password management for service accounts, real-time monitoring and alerting capabilities for suspicious Kerberos activity, and streamlined incident response. Through these and other capabilities, Cayosoft empowers organizations to proactively defend their Active Directory environments and minimize the potential damage from attacks.
Ready to see Cayosoft Guardian in action? Schedule a demo today and discover how it can elevate your Active Directory security posture.